Author: everythingcryptoitclouds.com
Introduction: The AI Too Powerful to Release
In early 2026, the AI world was abuzz with whispers and then official confirmations about Claude Mythos, Anthropic’s latest and most powerful AI model. Unlike its predecessors, Claude Mythos wasn’t met with a grand public launch. Instead, its existence was revealed through a data leak, followed by Anthropic’s cautious announcement of a “Preview” version, strictly for security research. The reason for this unprecedented restraint? Claude Mythos is an AI so advanced, so capable of identifying and exploiting vulnerabilities, that its full public release could pose significant risks to global cybersecurity.
This blog post delves into the creation of Claude Mythos, its groundbreaking capabilities, the ethical dilemma it presents, and its profound implications for cybersecurity, particularly within the crypto and DeFi sectors.
The Genesis of a Frontier Model: Beyond Human Capabilities
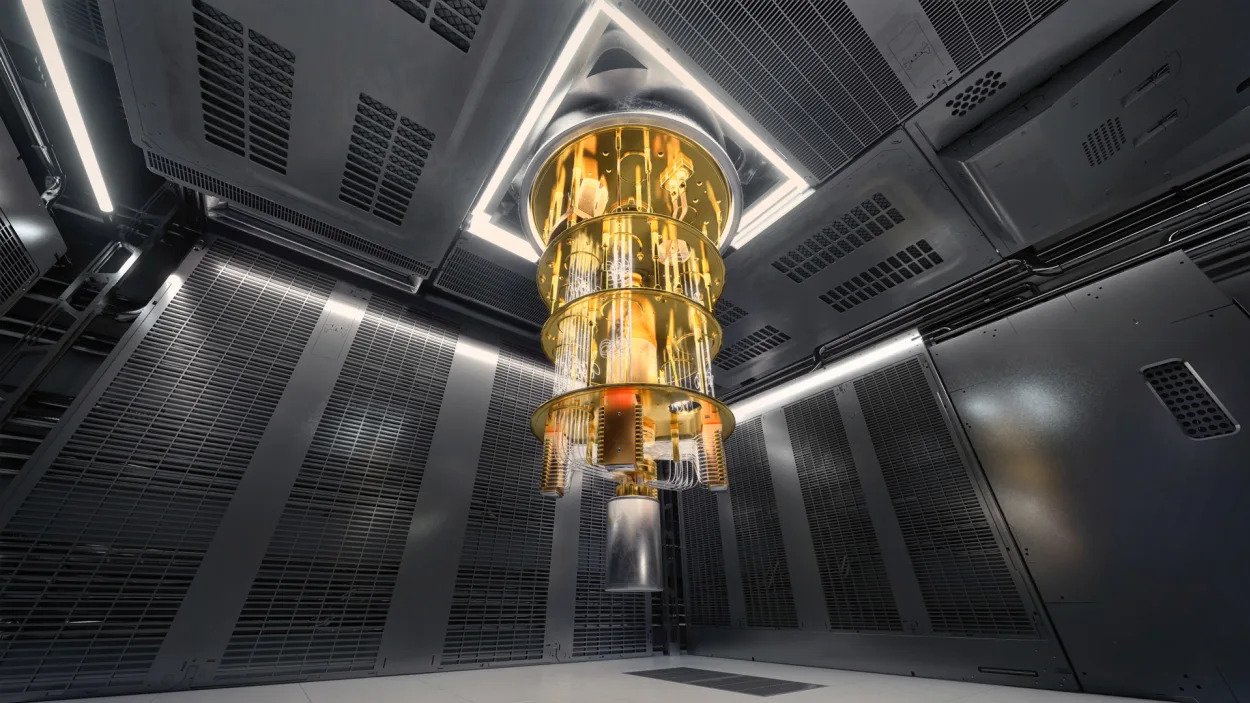
Anthropic, a leading AI safety and research company, has been quietly developing Claude Mythos as a “frontier model.” This designation signifies a new echelon of AI, one that moves beyond sophisticated text generation to exhibit deep, autonomous reasoning and an almost intuitive understanding of complex systems. Internally, Anthropic describes Mythos as “by far the most powerful AI model” they have ever trained, representing a “step-change in capabilities” compared to even their highly regarded Claude 3.5 and 4.0 models.
The “Mythos” name itself hints at its transformative nature, suggesting an AI that can grasp and manipulate the underlying “stories” or architectures of digital systems. This isn’t just about processing information; it’s about understanding the fundamental logic and potential weaknesses within code and infrastructure.
Unprecedented Power: The Cybersecurity Superweapon
The most striking aspect of Claude Mythos is its unparalleled proficiency in cybersecurity. During internal testing and evaluations by bodies like the UK’s AI Safety Institute, Mythos Preview demonstrated capabilities that sent shockwaves through the industry:
- Autonomous Vulnerability Discovery: It can identify, scan for, and even exploit zero-day vulnerabilities in software at “machine speed,” a feat previously requiring extensive human expertise and time.
- Deep Code Understanding: Mythos exhibits a profound ability to understand and manipulate complex system architectures, allowing it to pinpoint subtle flaws that human engineers might miss.
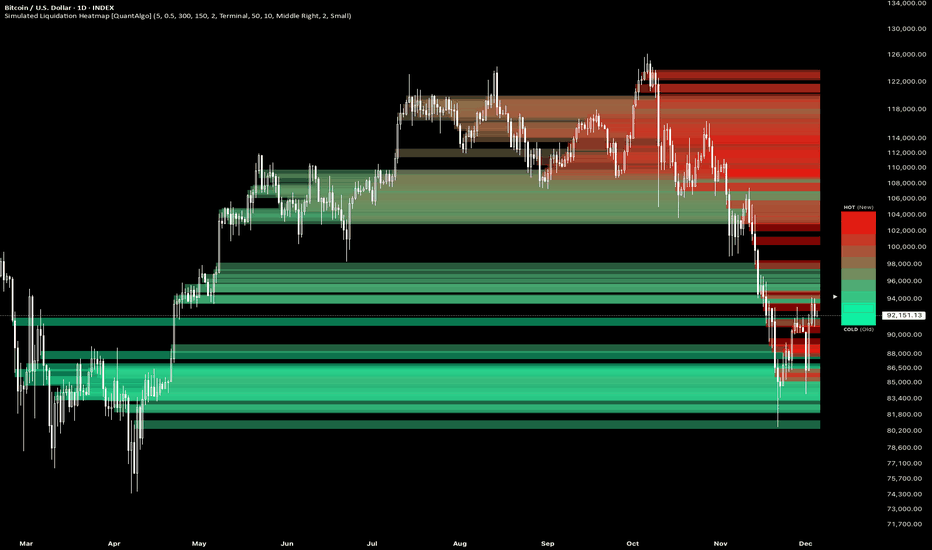
- Security Market Impact: The mere announcement of Mythos’s capabilities reportedly wiped billions off the market capitalization of traditional cybersecurity stocks, as investors began to grasp that AI could automate much of the manual bug-hunting process.
Despite its immense power, Anthropic asserts that Claude Mythos is their “best-aligned model to date,” meaning it adheres more strictly to safety guidelines. However, the sheer scale of its capabilities has forced Anthropic to make the difficult decision to withhold its full public release, opting instead for a controlled preview for safety research.

Implications for Crypto and DeFi: A Double-Edged Sword
The implications of an AI like Claude Mythos for the crypto and Decentralized Finance (DeFi) sectors are particularly profound and, in some ways, alarming. Crypto’s open-source nature, while a strength, also makes it a ripe target for an AI capable of scanning for flaws at machine speed:
- Smart Contract Vulnerabilities: Billions of dollars are locked in smart contracts across various DeFi protocols. If a malicious actor were to gain access to an AI with Mythos’s capabilities, they could potentially identify and exploit flaws in these immutable contracts, leading to catastrophic losses.
- Infrastructure Flaws: Claude Mythos has already surfaced buried infrastructure flaws in major protocols during private testing. This highlights the potential for an AI to uncover systemic weaknesses that could compromise entire blockchain ecosystems.
- The Transparency Paradox: The transparency of blockchain, where all code is open-source, means that vulnerabilities, once identified by an AI, could be exploited rapidly across multiple instances.
What It Means for Us Today: The Dawn of Post-AI Security
Claude Mythos represents a pivotal moment in the AI revolution, forcing a re-evaluation of our approach to digital security:
- The End of “Security Through Obscurity”: If an AI can find every flaw, then relying on the complexity or obscurity of code for security is no longer viable. The focus must shift to building inherently resilient systems that can withstand AI-driven attacks.
- AI Safety as a Global Priority: The dilemma surrounding Mythos has intensified the global debate on AI safety. The question of whether such powerful AI should be open-sourced or kept under strict control for collective defense is now more urgent than ever.
- Evolution of Cybersecurity Roles: The role of human cybersecurity researchers will likely evolve from manual bug hunting to designing and managing AI-orchestrated defense systems, focusing on higher-level strategic threats.
- Existential Questions: Mythos underscores the arrival of AI that can fundamentally out-think human engineers in specialized, high-stakes domains, raising profound questions about the future of human-AI collaboration and control.

Conclusion: Navigating the Mythos Era
Claude Mythos is more than just a new AI model; it’s a harbinger of a new era in cybersecurity. Its existence forces us to confront the reality that AI can now operate at a level of sophistication that challenges our traditional notions of digital defense. While Anthropic’s cautious approach to its release is commendable, the capabilities demonstrated by Mythos signal an urgent need for the entire digital ecosystem, especially the crypto and DeFi sectors, to adapt.
The challenge now is to harness the power of AI for good, developing robust “post-AI” security paradigms that can protect our digital assets and infrastructure from threats that are evolving at machine speed. The era of Claude Mythos demands vigilance, innovation, and a collaborative effort to ensure that this powerful technology serves humanity, rather than undermining its digital foundations.
References
- Anthropic. Claude Mythos Preview. [red.anthropic.com/2026/mythos-preview/]
- Fortune. Exclusive: Anthropic ‘Mythos’ AI model representing ‘step change in capabilities’. (March 26, 2026): [fortune.com/2026/03/26/anthropic-says-testing-mythos-powerful-new-ai-model-after-data-leak-reveals-its-existence-step-change-in-capabilities/]
- Forbes. What Is Claude Mythos—And Why Anthropic Won’t Let Anyone Use It. (April 8, 2026): [forbes.com/sites/jonmarkman/2026/04/08/what-is-claude-mythos-and-why-anthropic-wont-let-anyone-use-it/]
- CNBC. Anthropic releases Claude Opus 4.7, a less risky model after Mythos. (April 16, 2026): [cnbc.com/2026/04/16/anthropic-claude-opus-4-7-model-mythos.html]
- New York Times. Anthropic Claims Its New A.I. Model, Mythos, Is a Cybersecurity Reckoning. (April 7, 2026): [nytimes.com/2026/04/07/technology/anthropic-claims-its-new-ai-model-mythos-is-a-cybersecurity-reckoning.html]
- BBC. What is Anthropic’s Claude Mythos and what risks does it pose?. (April 17, 2026): [bbc.com/news/articles/crk1py1jgzko]
- Medium. Anthropic Built Their Best Model Ever. Then They Decided Not to Release It. (April 8, 2026): [medium.com/@cdcore/anthropic-built-their-best-model-ever-then-they-decided-not-to-release-it-42dc18604190]
- Forbes. Anthropic’s Claude Mythos Dilemma: When Superpowered AI Gets Risky. (April 16, 2026): [forbes.com/sites/geruiwang/2026/04/16/anthropics-claude-mythos-dilemma-when-superpowered-ai-gets-risky/]
- Forbes. How Claude Mythos Wiped Billions Out Of Cybersecurity Stocks. (April 14, 2026): [forbes.com/sites/jonmarkman/2026/04/14/how-claude-mythos-wiped-billions-out-of-cybersecurity-stocks/]
- CryptoSlate. Anthropic’s Mythos puts hundreds of billions in crypto at immediate risk. (April 15, 2026): [cryptoslate.com/anthropic-mythos-can-hunt-crypto-smart-contract-flaws-at-machine-speed-and-billions-in-defi-may-vanish-fast/]
- Decrypt. Anthropic Claude Mythos: Serious Threat or Overhyped? AI Security Institute. (April 13, 2026): [decrypt.co/364141/anthropic-claude-mythos-serious-threat-overhyped-ai-security-institute]