Author: everythingcryptoitclouds.com
Introduction: A Black Saturday for DeFi
April 18, 2026, will be remembered as a dark day in decentralized finance (DeFi). A sophisticated exploit targeting KelpDAO, a liquid restaking protocol, led to the draining of approximately $292 million in rsETH (restaked Ether) from its LayerZero-powered cross-chain bridge. The fallout was swift and severe, cascading through the DeFi ecosystem and leaving Aave, one of the largest lending protocols, grappling with an estimated $177 million to $200 million in bad debt in its wETH pool. This incident, now the largest DeFi hack of 2026, has sent shockwaves through the community, prompting urgent calls for users to withdraw funds and raising critical questions about the security and interconnectedness of DeFi protocols.
This blog post will dissect the KelpDAO exploit, its immediate and long-term implications for Aave and the broader DeFi landscape, and the lessons that must be learned from this latest crisis.
Anatomy of an Exploit: How $292 Million Vanished
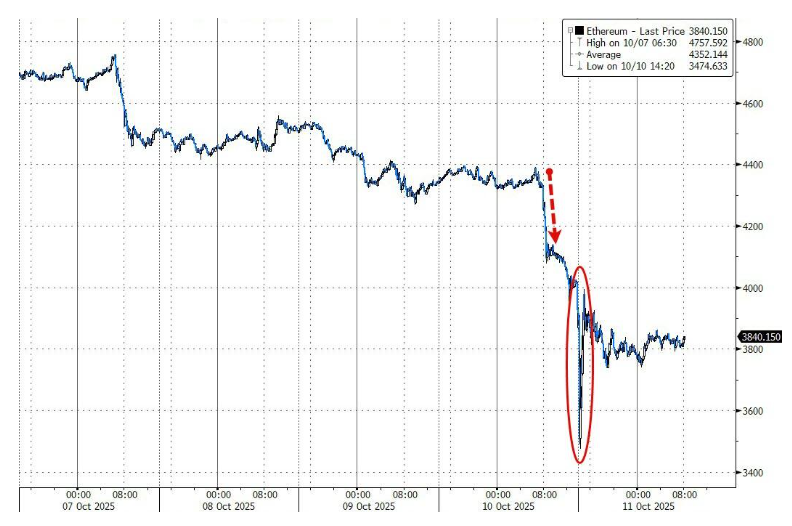
The attack, which occurred at 17:35 UTC on Saturday, April 18, 2026, exploited a critical vulnerability in KelpDAO’s LayerZero-powered bridge. LayerZero is a cross-chain messaging layer designed to facilitate communication and asset transfers between different blockchains. The attacker cleverly tricked LayerZero’s validation logic, making it believe a legitimate instruction had arrived from another network. This deceptive maneuver caused Kelp’s bridge to release 116,500 rsETH—representing roughly 18% of rsETH’s total circulating supply—directly to an address controlled by the attacker.
The speed of the attack was alarming. While Kelp’s emergency pauser multisig eventually froze the protocol’s core contracts 46 minutes after the initial drain, two subsequent attempts by the attacker to drain an additional 40,000 rsETH (worth approximately $100 million) were also initiated, though ultimately reverted. The incident highlights the razor-thin margins and rapid response times required to mitigate damage in the fast-paced world of DeFi.
The Ripple Effect: Aave’s Bad Debt Crisis
The true gravity of the KelpDAO exploit became apparent as its effects rippled through the interconnected DeFi ecosystem. The attacker, using the stolen rsETH, deposited it as collateral into Aave, a leading decentralized lending protocol, to borrow a significant amount of ETH. This action created a massive amount of bad debt within Aave’s wETH pool.
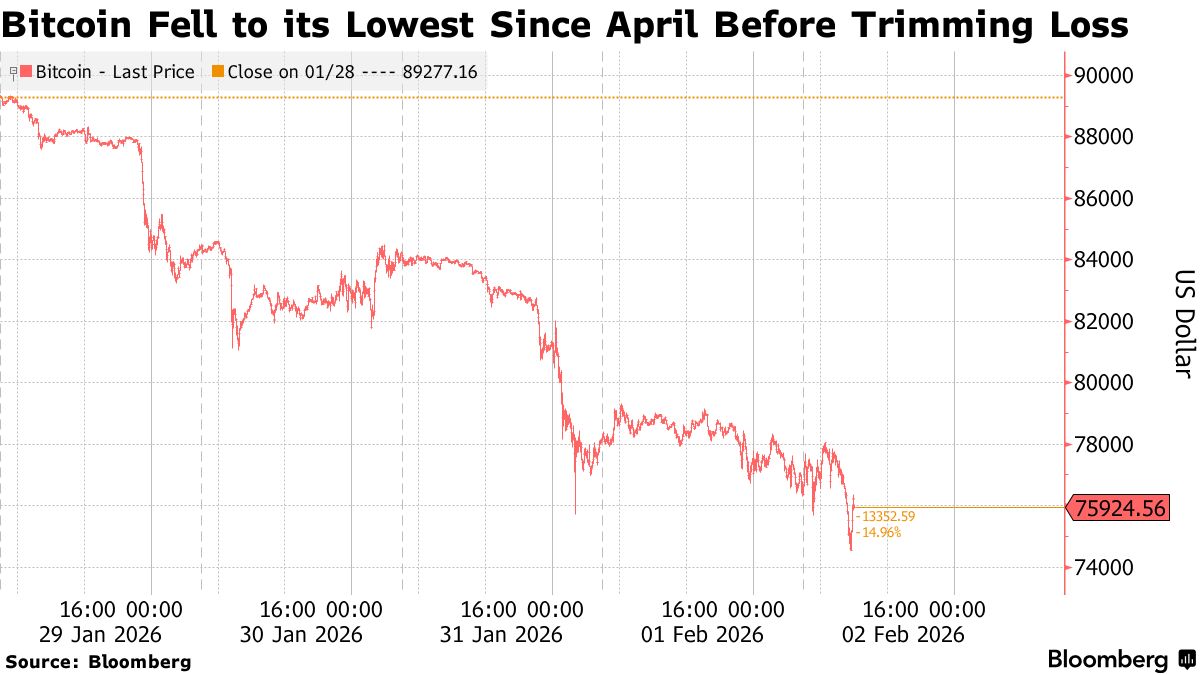
Bad debt arises when the collateral backing a loan loses significant value or becomes unrecoverable, leaving the borrowed assets without sufficient backing. In this case, the rsETH used as collateral was effectively compromised, leading to an estimated $177 million to $200 million in unbacked loans. The crisis immediately pushed Ethereum utilization on Aave to 100%, meaning legitimate wETH suppliers were unable to withdraw their funds, trapping their assets in the affected pool.
In response, Aave quickly froze rsETH markets on both its V3 and V4 platforms. Other protocols with exposure, such as SparkLend and Fluid, followed suit, freezing their own rsETH markets. Lido Finance, a major liquid staking provider, paused further deposits into its earnETH product, which carries rsETH exposure, though it clarified that its core stETH and wstETH products remained unaffected. The market reacted sharply, with the AAVE token experiencing a roughly 10% price crash as investors priced in the potential losses and uncertainty.

Community Response and the Path Forward
The immediate aftermath saw a flurry of activity and concern across the DeFi community. Analysts and community members urged Aave wETH suppliers to withdraw their funds, a difficult task given the 100% utilization. Discussions quickly turned to Aave’s “Umbrella” safety module, a mechanism designed to cover bad debt in extreme circumstances. The activation and parameters of this module are now a critical point of debate and decision for the Aave DAO.
The incident also underscored the inherent risks of liquid restaking tokens and cross-chain bridges. With rsETH deployed across more than 20 networks, including major Layer 2 solutions like Base, Arbitrum, and Linea, the exploit raised serious questions about the backing of rsETH on all these deployments. The contagion risk is significant, as panic redemptions on Layer 2s could further pressure the unaffected Ethereum supply.
Lessons from the Latest DeFi Crisis
The KelpDAO exploit serves as a stark reminder of the vulnerabilities inherent in the rapidly evolving DeFi landscape:
- Interconnectedness Amplifies Risk: The incident demonstrates how a single exploit in one protocol can trigger a cascading crisis across multiple interconnected platforms, highlighting the need for robust risk management across the entire ecosystem.
- The Challenge of Cross-Chain Security: Cross-chain bridges, while essential for interoperability, remain a significant attack vector. Ensuring the integrity of messaging layers like LayerZero is paramount.
- Importance of Decentralized Governance and Rapid Response: While KelpDAO’s emergency pauser was activated, the speed of the exploit still allowed for massive losses. The balance between decentralization and the ability for swift, decisive action in a crisis remains a critical challenge.
- Due Diligence for Users: The incident reinforces the importance for users to understand the risks associated with various DeFi protocols, especially those involving liquid staking and cross-chain assets. The advice to “withdraw now” underscores the need for constant vigilance.
Conclusion: A Call for Enhanced Security and Resilience
The KelpDAO exploit and the resulting bad debt in Aave’s wETH pool are a painful but necessary lesson for the DeFi industry. As the largest hack of 2026, it underscores the urgent need for enhanced security audits, more resilient cross-chain infrastructure, and improved risk management frameworks across all protocols. The community’s ability to navigate this crisis, settle the bad debt, and implement stronger safeguards will be crucial for restoring confidence and ensuring the long-term sustainability of decentralized finance.
The path forward requires collaboration, innovation, and a renewed commitment to security. Only by learning from these costly incidents can DeFi truly mature and fulfill its promise of a more open and equitable financial system.
References
- CoinDesk. Kelp DAO exploited for $292 million with wrapped ether stranded across 20 chains. (April 19, 2026): [coindesk.com/tech/2026/04/19/2026-s-biggest-crypto-exploit-kelp-dao-hit-for-usd292-million-with-wrapped-ether-stranded-across-20-chains]
- Yahoo Finance. Aave WETH Suppliers Urged to Withdraw After KelpDAO Exploit Creates $200M Bad Debt. (April 19, 2026): [finance.yahoo.com/markets/crypto/articles/aave-weth-suppliers-urged-withdraw-194751997.html]
- Cryptopolitan. Kelp DAO exploited for $292 million with wrapped ether stranded across 20 chains. (April 19, 2026): [cryptopolitan.com/hyperunit-whales-gain-turn-to-250m-loss/]
- Crypto Briefing. KelpDAO exploit causes AAVE ETH pool to utilization. (April 19, 2026): [cryptobriefing.com/kelpdao-exploit-causes-aave-eth-pool-to-utilization/]
- Forbes. AAVE wETH Exploit: $200M Bad Debt Hits Depositors. (April 18, 2026): [forbes.com/sites/digital-assets/2026/04/18/withdraw-now-inside-aaves-sudden-200m-bad-debt-crisis/]
- MEXC. AAVE Price Crashes 10% as Aave’s KelpDAO Faces $280M Exploit. (April 19, 2026): [mexc.com/news/1037203]
- Intellectia.ai. The Biggest DeFi Hack of 2026: $293 Million Lost in 46 Minutes. (April 19, 2026): [intellectia.ai/news/crypto/the-biggest-defi-hack-of-2026-293-million-lost-in-46-minutes]
- CryptoNews.net. Kelp DAO Bridge Drained for $292M in 2026’s Biggest DeFi Hack. (April 19, 2026): [cryptonews.net/news/defi/32729015/]
- Binance Square. Kelp DAO Faces Attack Amid Aave’s Bad Debt Concerns. (April 19, 2026): [binance.com/en/square/post/314034493954657]